Understanding How GNSS Spoofing and Jamming Threaten Global Aviation Safety
- GPS and other Global Navigation Satellite Systems (GNSS) form the backbone of modern navigation for aviation and maritime sectors, making them highly vulnerable to interference.
- Spoofing and jamming — deliberate radio-frequency attacks — can disrupt or manipulate navigation data, posing serious safety risks.
- Growing incidents near conflict zones highlight the urgent need for robust detection and mitigation technologies to safeguard global flight operations.
An Air India flight operating from Vienna to Delhi was forced to divert to Dubai after experiencing severe GPS interference in October 2025.
The interference impacted aircraft’s navigation and control systems, causing the autopilot, auto-thrust, flight director and its Autoland systems to malfunction. Pilots had to manually fly the aircraft after that.
Many more such incidents have been reported wherein GPS interference adversely affected aircraft (and marine traffic) movement.
One incident which captured the attention of the global aviation community happened in Europe, when a plane carrying European Union Chief Ursula von der Leyen was reportedly forced to land in Bulgaria using paper maps after its GPS was unauthorisedly jammed. Interference of GPS signals have increased significantly in recent years. The following section provides a brief overview of the subject.
GNSS functioning
Starting with the launch of the full constellation of 36 satellites in 1968, the Global Positioning System (GPS) came into operation for enhancing the navigation capability of the US Navy. Shortly thereafter, the USSR (now Russia) launched its own system, GLONASS, followed by the European Union launching Galileo and China launching BeiDou.
In addition to these global systems, two more regional systems, NavIC (Navigation with Indian Constellation) by India and QZSS (Quasi-Zenith Satellite System) by Japan, also exist now to provide navigational information in their local airspace. Collectively, these systems are called the Global Navigation Satellite System or GNSS.
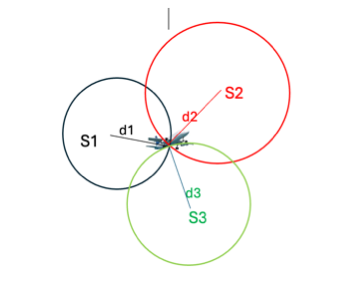
GNSS works on the principle of triangulation (Fig. 1), wherein an airborne receiver calculates the time of travel (converted to distance) of coded signals from at least three satellites and derives its position in space in terms of X, Y and Z coordinates.

Clocks provided in commercial receivers are not very stable and accurate (to save on cost) and since accuracy of the positional and time information depends on the accuracy of time provided by receiver clock (satellite clock being much more stable and time correction broadcast by individual satellite), time bias in receiver clock needs to be corrected which is done by using distance from a fourth satellite as an additional variable (Fig. 2) in the matrix.
GNSS has now become the main tool for global navigation, both for aircraft and for marine traffic, and hence any threat of broadcasting misleading information or stoppage of its service can have a catastrophic effect.
Two types of threats to the integrity of GNSS have been observed:
Spoofing
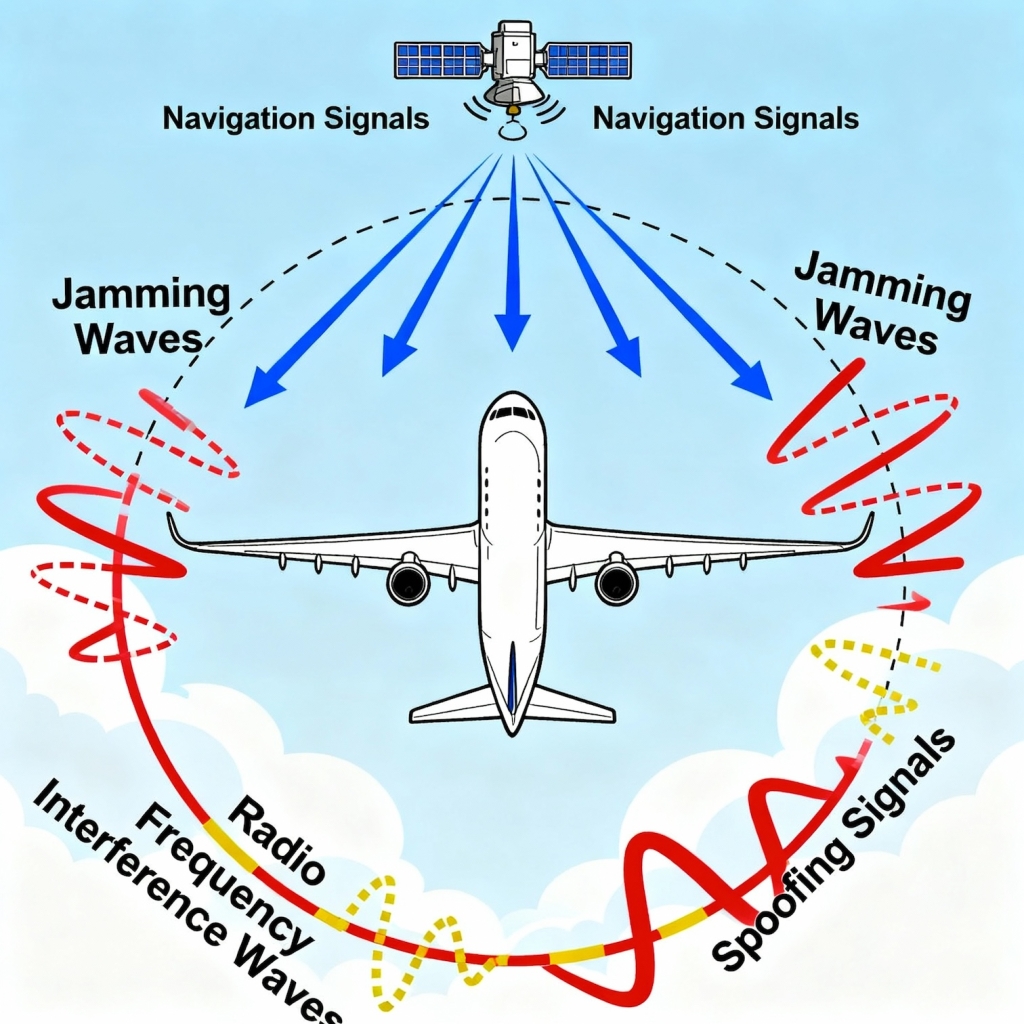
It is a deliberate broadcast of fake signals to deceive a receiver into calculating incorrect data, such as false positional information.

It is an intentional activity to mislead the receiver by feeding it incorrect data, resulting in false position, navigation, and/or timing information without immediate signal loss (Fig. 3).
Although these counterfeit signals resemble the genuine signal, they may differ in various ways to fool the GPS receiver:
- Code (and carrier) phase drift.
- Incorrect orbit biases that alter the position completely, or setting some/all visible satellites to unhealthy.
- Incorrect timestamp from each satellite, which will change position, altitude, speed, time and date information.
Most of the modern aircraft have incorporated GPS into aircraft systems as a tool for long-distance navigation. Spoofing is mainly used by military units targeting hostile aircraft/drones and drone swarms. Sometimes, it is used by the Police, Public Safety and National security agencies for preventing the use of drones at events.
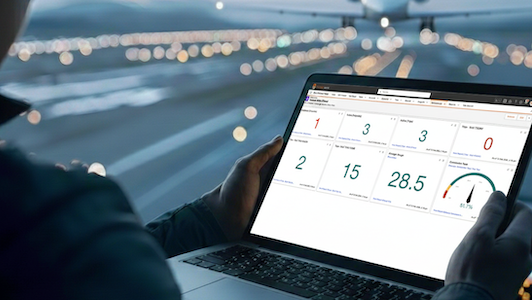
As per the report submitted in ‘OPSGROUP GPS Spoofing WorkGroup 2024’, in one month (July 15 to August 15, 2024), a total of 41,000 flights experienced spoofing. Impact of a spoofed GPS (GNSS in general) signal, in addition to providing misleading positional information in the cockpit, also has a cascading effect on other aircraft systems (which may include FMS, Hybrid IRS, the aircraft clock, GPWS, Weather Radar, CPDLC, ADS-B and ADS-C and some other systems).
Spoofing began to severely impact civil aviation in September 2023 in northern Iraq, centred on Baghdad. Even though GPS interference is not a new phenomenon, the scale and effects of the current wave of spoofing are unprecedented. By January 2024, an average of 300 flights a day were being spoofed, and by August 2024, this had grown to around 1500 flights per day.
As per the OPSGROUP Report, almost all current GPS spoofing incidents are affecting civil aircraft in and around the conflict zones, and it has also been observed in different parts of the world, including/India-Pakistan border area.
As of now, spoofing seems to be affecting the performance of US GPS only; too many reports of its adverse effects on other GNSS options have not been observed so far. For example, Indian Regional GNSS, NavIC, was used for targeting military targets in Pakistan very precisely during Sindoor operations.
Jamming
It is an intentional/unintentional interference with GNSS signals to block them and make them unstable, resulting in Denial of Service.
Jamming signal completely shadows the genuine GNSS signal, and hence the cockpit display goes blank (Fig. 4). It prevents devices from receiving legitimate signals, causing them to lose their ability to derive correct information completely.

Jamming signals prevent receivers from locking onto satellite signals and have the main effect of rendering the GNSS system ineffective or degraded in the jammed area. The simplest and most effective method used by intentional jammers is to transmit a Continuous Wave (CW) RF signal in the GNSS band.
For example, an attacker can transmit a CW signal on L1 frequency (1,575.42MHz) and effectively block legitimate GPS signal.
GNSS receivers, which use GPS, GLONASS, Galileo, BeiDou, QZSS or NavIC signals, are notably vulnerable, and this is because of the nature of the signals which emanate from orbiting satellites located around 20,000km above the earth’s surface.
The signal received is very weak, but it is still workable if there is no interference. Interference could be unintentional (like by Ligado, an American SatCom terrestrial network which uses the same L-Band Spectrum as GPS) and intentional Jamming of the frequency by activating ground-based transmitters radiating strong RF signals in the same frequency band.
Another common example of unintentional jamming is the organizing of drone shows which use RF control signals. Spoofing and Jamming, two distinct forms of radio frequency interference that affect GNSS can be differentiated as follows:
| Features | Spoofing | Jamming |
| Methodology | An adversary broadcasts counterfeit GNSS signals designed to deceive a receiver into calculating a false position and/or time. | An adversary broadcasts powerful radio signals on GNSS frequency bands to disrupt or completely overpower legitimate satellite signals. |
| Effect | The receiver trusts false data, computes an incorrect position and time and can be tricked into following a malicious trajectory. | The receiver loses its ability to calculate an accurate position by showing a loss of signal or degraded service. |
| Detection | Harder to detect because the receiver believes it is receiving valid data and may not show any error. This makes it a more insidious and potentially dangerous attack. | Easier to detect, as the receiver will typically alert the user to a signal loss or degraded service. |
| Complexity | Requires more sophisticated equipment and knowledge to properly mimic authentic signals and control the receiver. | Simple and inexpensive to execute. Devices that can be used for jamming are available commercially also. |
Mitigation Techniques
Whereas there are individuals and agencies working to disrupt air traffic by spoofing and jamming techniques, there are agencies which are involved in protecting operations on the other end. Some of the mitigation techniques they adopt include signal processing methods, data bit methods, position methods and machine learning/deep learning methods.
Also Read: Enhancing Precision: India’s NavIC System